iPads don’t have to add risk
Tools & techniques prevent leaks
- |
- Written by Joe Oleksak and Colin Taggart, Plante Moran

Since its debut in April 2010, the iPad quickly became the most popular tablet, outselling all competitors in the market combined. With the newer models flying off the shelves, the number of iPad owners continues to soar.
Banks have been impacted by iPads from several perspectives. For example, financial institutions are adopting the iPad to distribute board of director meeting information electronically, while front-line employees are also using the iPad to walk customers through mobile banking application functionality.
With the introduction of any new technology, however, comes risk. As such, many IT departments are reluctant to provision iPads for board members and employees. But that is changing. The company’s updates to the iOS (operating system) have helped achieve greater acceptance by including many security features, such as application-level encryption and the ability for organizations to impose security policies on company-owned iPads.
What follows are answers to some commonly asked questions surrounding the organization-wide management of iPads.
Q. How can financial institutions best manage applications at the employee level?
A. Once the excitement of getting iPads settles in, the anxiety of managing these devices kicks it. You can do it the hard way (manually), use configuration profiles, or use a mobile device management (MDM) solution.
The obvious choice would be to use a MDM. A MDM allows you to simultaneously control and configure a large pool of iPads. The magical app that does this for free is Apple Configurator. This application allows you to create “groups of devices” and manage each group independently with their own configuration profile.
When it comes to application ownership model, there are three models:
• Personal—users can install.
• Institutional—company owns application license.
• Layered or shared model—where company and the user can install applications.
The Apple Configurator allows you to purchase and deploy applications; create device and user groups, create a master or template for a group; and push the configuration to other (iPads) in the group and check-in/check-out devices to users.
Q. What authentication parameters are available on the iPad, and can I enforce secure passwords on the iPad centrally?
A. The iPad’s operating system allows system administrators to employ the same type of authentication parameters used in most information security policies. The following authentication settings are configurable on the iPad:
• Require passcode on device
• Allow simple value
• Require alphanumeric value
• Minimum passcode length
• Minimum number of complex characters
• Maximum passcode age
• Auto-lock
• Passcode history
• Grace period for device lock
• Maximum number of failed attempts
Employing these authentication parameters centrally can be achieved with the use of third-party MDM software. In order to distribute a policy across multiple devices, a configuration profile can be installed on each device that manages security settings.
This configuration profile can be protected from alteration by the end user by restricting access to the profile with the use of an administrator password, so only authorized individuals can make changes to the settings. Configuration profiles used in conjunction with MDM allow an administrator to make configuration changes centrally and push the updates out to users without the need of any interaction from the end user.
Q. What logging settings are available on the iPad?
A. The iPad does not have built-in logging capabilities. However, with the use of third-party MDM software several different types of activity can be logged and monitored. Applications are available for the iPad that allow financial institutions to centrally log and monitor the following types of activities:
• Unauthorized attempts to access secure networks
• Types of devices accessing the network
• Users authenticating to the network
• Applications installed on devices
• GPS location
• Device information
• Compliance and security information
Q. Should security for mobile devices like the iPad be included in annual security awareness training?
A. The use of devices like the iPad in a financial institution pose several risks specific to the device (largely due to its mobility) that should be communicated to staff to ensure that the appropriate precautions are taken to secure your organization’s information.
Before distributing iPads to board members or employees, they should be provided mobile device security training and required to agree to a mobile device acceptable usage policy. Similar to annual information security training requirements, these employees should also receive mobile device security training information annually.
Q. Are there iPad security training programs for IT administrators?
A. Most vendors of MDM software offer training programs for its management systems. In some cases, vendors have created webinars that show the capabilities of their MDM products and, in turn, explain how the products are administered.
Q. Can I limit my staffs’ ability to download applications (apps), or are there any security risks by letting them download whatever they want?
A. End users can be restricted from downloading apps with the use of MDM software or the built-in parental controls. Most MDM software suites include the ability to completely restrict a user’s ability to download apps. Some have options to make only approved apps available for download with the use of a configurable app market.
The apps located in the Apple App Store are required to go through a screening process before they enter the market; however, in the past, apps have made it through Apple’s code review process only to be later pulled for performing actions that Apple does not permit. This will occasionally occur despite Apple’s best efforts. Allowing staff to “jailbreak” and install any apps they want could result in the propagation of malicious code across your entire network.
Q. Can iPads be jailbroken like iPhones? How do I prevent end users from doing that?
A. Many iDevice users may have heard of the term “jailbreaking” at some point. Jailbreaking allows users to gain full access and bypass built-in security features of the operating system.
Jailbreaking utilities such as PwnageTool, redsn0w, and JailbreakMe.com have made it easier for even the least technical user to crack open the iPad and install software through unofficial channels.
Financial Institutions should understand the potential security threats of jailbroken devices and implement strict controls to prevent it.
In addition to restricting a user’s ability to install applications, websites, or explicit media content, most MDM software also provides scanning capabilities to detect whether the operating system has been compromised. As an additional layer of control, staff should also be trained on the risks of jailbreaking their devices and how it could potentially lead to a compromise of confidential information.
Q. Does the concept of “Local Administrator” apply? Can end users surpass organization policies?
A. The iPad’s operating system restricts users from creating multiple user accounts. While this may be a limitation in some sense, it also effectively eliminates the risk of end users having local administrator account privileges. As long as devices are appropriately configured and enforced, administrators can be reasonably assured that iPad users cannot bypass organization policies.
Q. Is there a secure mechanism for board members and employees to connect to our internal network remotely?
A. The iPad’s built-in VPN client currently supports the following VPN protocols by default:
• SSL VPN
• Cisco IPSec
• L2TP over IPSec
• PPTP
In addition, third-party software can be installed that allows for additional protocol support.
Q. How do backups work? How do I ensure backups occur as scheduled?
A. Users can use iTunes to synchronize (sync) iPad data onto a laptop or workstation, and vice versa. iTunes creates a backup of iPad’s data and configurations via the iTunes sync process and offers a restore feature for users wishing to return to a previously backed up state. Users can also use the backup and restore features to transfer information from one device to another.
It should be noted that iTunes keeps only one backup for each device.
iTunes can be configured to automatically launch the sync process every time an iPad is connected to the computer. Similarly, iPad backups should be configured to require encryption using Apple’s iPhone Configuration Utility.
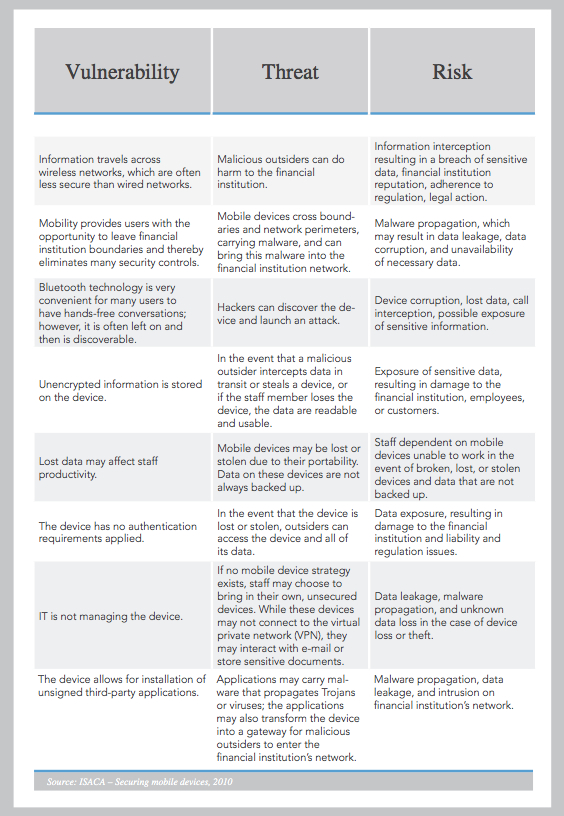 For a larger version, click on the image.
For a larger version, click on the image.
Another important feature of the operating system is the availability of iCloud services. This allows the iPad to send backups and other data to Apple’s servers and could violate the privacy provisions of the Gramm-Leach-Bliley Act, the Health Insurance Portability and Accountability Act, or the Health Information Technology for Economic and Clinical Health Act. The most recent version of iPhone Configuration Utility added options to block some iCloud choices. It is recommended that companies use Apple’s configuration utility to disable iCloud backups, iCloud documents and data, and photo stream.
Without an enforceable way to require iPad backups, policies and procedures continue to play a significant role in backup management. Financial institutions should communicate to end users the importance of frequent, periodic backups, and discourage the creation and/or storage of confidential or critical information on mobile devices like the iPad whenever possible.
A powerful possibility
There are many things that need to be taken into consideration when looking at “incorporating” the iPad, but we have to remember that the majority of these security implications are going to be addressed for any new technology. The main security risk that the iPad poses is its mobility and the decentralization of information, but there are ways to secure it and with business going mobile, this device can be a powerful tool.
Organizations should be well versed in the security implications an iPad brings to the table but they should also be aware that they’re no greater with the iPad than with any other emerging technology. And it appears that this one’s here to stay.
About the authors
Joe Oleksak is principal in the information technology consulting practice at Plante Moran. He can be reached at [email protected]
Colin Taggart is senior consultant in the information technology consulting practice at Plante Moran. He can be reached at [email protected]
Related items
- Banking Exchange Hosts Expert on Lending Regulatory Compliance
- Merger & Acquisition Round Up: MidFirst Bank, Provident
- FinCEN Underestimates Time Required to File Suspicious Activity Report
- Retirement Planning Creates Discord Among Couples
- Wall Street Looks at Big Bank Earnings, but Regional Banks Tell the Story













