Capturing all risk tasks "with one elephant"
Final part of series: Can any one system contain the whole risk management challenge?
- |
- Written by Ken Proctor
 Risk management expert Ken Proctor of Abound Resources doesn’t believe the risk management information system exists yet that will entirely serve the chief risk officer’s complete need
Risk management expert Ken Proctor of Abound Resources doesn’t believe the risk management information system exists yet that will entirely serve the chief risk officer’s complete need
Six blind men are asked to describe what an elephant is like. In order to answer the question, each touches the beast. The one touching a leg declares that the elephant “is like a pillar.” Another, touching the ear, declares the elephant to be like a “fan.” A third, touching the elephant’s tail, declares the pachyderm “like a rope.”
Each described the elephant from their own limited perspective, reaching very different conclusions.
Selecting or building an enterprise risk management information system (ERMIS) solution is much like describing that elephant. Depending on one’s perspective, what an ERMIS should look likes varies widely. Similarly, vendors will insist that their elephant is all that an elephant should be.
In my experience, no one ERM software package has yet become “the elephant.”
No package offered today meets all the requirements of a comprehensive, effective risk management information system. Several are close, and they are becoming better.
Let’s examine what you should be striving for and how it should work.
ERM system functionality
Many banks are developing tools in-house, using Excel, Access, or Sharepoint for their building blocks. But as bankers have learned, risk tools developed this way fall short. They become information silos, are not always accurate, duplicate information developed in other business units and generally require a level, sometimes a significant level, of manual input or data “massaging.”
There are multiple needs to be addressed by an ERMIS, and different solutions may be required to address them. However, there are three critical elements of an effective ERMIS that both align with regulators’ expectations and that provide a comprehensive, effective risk management information solution for banks:
• Risk and control assessment
• Risk control management
• Risk modeling/forecasting
Risk and Control Assessment
Risk assessments typically prioritize or rank items or events. At a minimum, an ERMIS should facilitate the preparation of the various risk assessments required by the regulators, such as BSA/OFAC, Information Security, ID theft, and Vendor Management.
The system, particularly commercial off-the-shelf solutions, should provide easy-to-use templates. Beyond basic regulatory risk assessments, it would also be helpful if they provided risk assessment templates for Compliance, Internal Audit, Physical Security, and Information Technology. Also useful: Business Impact and Threat Analysis tools to support business continuity and disaster recovery plans.
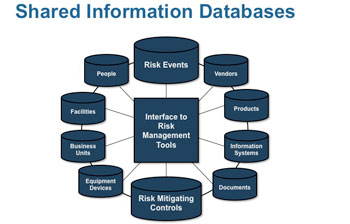
Whether your bank builds or acquires an ERMIS, you should consider, at a conceptual level, creating databases of information that can be shared by elements of the ERMIS, such as employees, information systems, business units, and other information. Examples of these information databases are included in the illustration below:
An ERMIS—Enterprise Risk Management Information System—should include a “library” of information accessible to those using the system to do their jobs, no matter where in the bank they work. (For a larger version of the chart, click on the image.)
Once these databases are created, the information can be accessed by the ERMIS tools through drop-down menus, making it much easier to develop risk assessments. The system should also facilitate updating and changing the information, such as employee names and assignments and ensure consistency, accuracy, and currency of information.
Beyond preparing base risk assessments, an ERMIS should permit the bank to identify specific risks and threats and document those controls and procedures that mitigate those risks. The system should permit risk categories and levels to be assigned to each risk. This would permit risks and related controls to later be segregated and printed, if needed, for analytical purposes (i.e., reports of compliance risk issues and related controls).
Further, the ERMIS should enable the bank to document features of those controls, such as where the control or procedures is documented; who is responsible for the control; and how often the control is performed and how the completion of the control is documented.
Look for labor-saving features everywhere you can. For example, risk managers and other users would find it extremely beneficial if other information about each control, such as whether it is required for Sarbanes-Oxley, FDICIA, and FCPA financial reporting risk assessments, was also captured.
This includes such information as: the control objective satisfied by the procedure; whether the control is automated or manual; and financial statement assertions related to the control. Users would save time and effort if documents could be scanned into the system.
Alternatively, the system could accommodate links to documents in the bank’s imaging system or insertion of hyperlinks to the internet, to be associated with risks, controls, and procedures. Consider the convenience of being able to immediately access procedural documentation or copies of relevant regulations.
Other important features of risk and control assessments include the ability to:
• Assign levels of inherent risk and exposure to a threat. Be sure to include how likely or how frequently this event might occur and what the impact of the event could be.
• Rank the effectiveness of the design of the control. How effective does the bank consider the control to be in mitigating either the likelihood of a particular event or the impact of an actual event.
• Assign levels of residual risk and exposure to a threat. After considering the effectiveness of the control, how likely or how frequent is this event likely to occur and what would be the likely impact of the event.
• Test the effectiveness of the control. This could include documenting the nature of the test, test population, and test result.
• Document compensating and complementary controls. The bank needs to have these in place to support controls where test results indicate a weakness.
• Reach a conclusion on the overall effectiveness of controls—primary and complementary or compensating—in mitigating a risk.
• “Freshness dating.” Finally, risk assessment should provide status information, such as whether assessments are complete and current.
Risk Control Management
An important limitation to understand about risk assessments is that, while they are informative, they are typically static—a snapshot in a point in time.
But risk must be actively managed.
This shortcoming of risk assessments can be reflected in accompanying systems. While banks deploy millions of dollars in technology systems, few of those systems are designed to manage the bank’s risk administration. Most were designed to manage transactions and customer relationships.
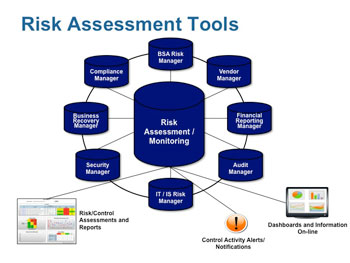
Key risk management tools that are typically part of the ERMIS are illustrated in the diagram below:
A true ERMIS presents the risk management side of the bank’s relationships and business activities. The stress must be on a dynamic approach, not static reporting. (For a larger version of the chart, click on the image.)
Critical risk management tools include business continuity planning, vendor management, and financial reporting (SOX 404, FDICIA, FCPA) management systems. Tools like BSA suspicious activity and fraud monitoring and case management systems are also included in the risk management system tool set.
The bank’s ERMIS should leverage information developed in the risk assessment, particularly information about controls and procedures, to actively manage risk. The bank’s risk officer should be able to monitor the completion of key risk controls on an ongoing basis.
For example, personnel assigned to key control responsibilities should note the completion of the control in the system. The system should issue alerts of controls not completed in a timely manner, and generate e-mails to the delinquent party. If documentation of the controls’ execution is uploaded into the system, such as a copy of the reconcilement document, account analysis, or test worksheet, it can be reviewed by the risk officer.
Risk Modeling/Forecasting
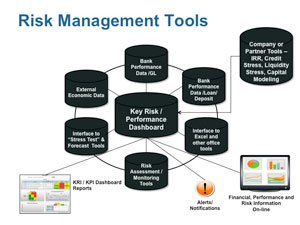
Increasingly regulators are requiring that banks deploy models to forecast future performance results. These models include interest rate shock, liquidity stress, credit risk, and capital forecasts. Each of these models are integral parts of the ERMIS, producing their own results, and contributing data to overall key risk indicator dashboards.
Each model requires certain external information, such as economic and interest rate data, and scenarios in the model are influenced significantly by the bank’s strategic objectives and risk appetite.
In many ways, the Key Risk Indicator Dashboard is the heart of the ideal ERMIS. (For a larger version of the chart, click on the image.)
These dashboards represent perhaps the most critical element of the ERMIS, and the culminating tool. Dashboards of leading and lagging KRI in the risk categories specified by regulators, such as credit, interest rate, market, liquidity, compliance, operational, reputational, and strategic risk, provide the vital information needed by management, and particularly by directors, to manage risk.
As I mentioned in the first article of this series, if business process factors are critical to the success of a particular strategic initiative, such as the growth of mortgage loans, then it is important that information be tracked to help management and directors understand why the indicator on the dashboard regarding mortgage loan production is trending one way or the other.
• For example, if the volume of mortgage loans is below the target, why?
• Is it the result of not generating enough applications?
• If plenty of applications are being generated, but they aren’t being approved, is it because they were withdrawn because processing took too long?
• Or were they rejected because the underlying credit was weak and should have been noted by the originator?
As management considers why the projected growth is not being achieved, this data will be critical to addressing the problem.
You have to balance the need for a complete picture with the chance of overwhelming the user in data—an overcrowded dashboard won’t be an assistance. I generally advise banks developing KRI dashboards to limit the number of key leading and lagging indicators in each risk category to around 14 to 16. I also advise them to develop indices of more detailed information to support certain of those KRI.
Meanwhile, back to the elephant
There is a corollary to the elephant parable. In this version, six blind elephants were discussing what men were like.
After arguing for awhile, they decided to find a man and determine what the biped was like by direct experience. The first blind elephant, feeling the man, declares that “men are soft and flat.” After each of the other blind elephants also feel the man, they agree.
Again, there are a number of systems and tools labeled as “enterprise risk management” solutions. None, in my opinion provide all the functionality covered here. Banks must carefully select and combine systems and tools from various vendors to implement a comprehensive and effective ERMIS solution.
Given this situation, the bank will need a roadmap, an architectural diagram, to ensure that these tools and systems work well together and that information silos are not created. Better to know ahead of time what you want to accomplish with an ERMIS and how it will be implemented than to have a group of elephants describe it.
• Part 1 of the series: Why risk management and strategic planning must synch
• Part 2 of the series: Re-engineering risk management from the ground up
Tagged under Management, Duties, Risk Management, Operational Risk, Feature,
Related items
- Banking Exchange Hosts Expert on Lending Regulatory Compliance
- Merger & Acquisition Round Up: MidFirst Bank, Provident
- FinCEN Underestimates Time Required to File Suspicious Activity Report
- Retirement Planning Creates Discord Among Couples
- Wall Street Looks at Big Bank Earnings, but Regional Banks Tell the Story